The MEV Layer Cake
Why Encryption Solves One Problem and Leaves Others

Encrypted mempools are increasingly adopted as a structural response to MEV. The protection they provide is real but bounded: systems operating under this model are often assumed to be shielded more broadly than they are, and the residual exposure lives in layers that encryption does not reach. This article examines what that protection covers, what it does not, and why real exposure cannot be assessed at a single layer.
It applies to any system that executes on-chain operations under an encrypted mempool model.
The Layer Cake
MEV exposure in a blockchain system is not a single surface. It is a stack of independent layers, each with its own attack vector and its own class of mitigations. A fix applied at one layer has no effect on the others.
Encrypted mempools target one layer of this stack directly. The others remain exposed, each for different reasons and through different mechanisms.

Consensus layer. The block producer controls which transactions are included and in what order. An adversarial producer can exploit this position independently of mempool visibility or transaction content.
Protocol layer. The rules governing transaction ordering, priority, and replacement within the node software. Vulnerabilities here do not require reading transaction content.
Mempool layer. The propagation and visibility of pending transactions before inclusion. This is the layer that encryption directly targets.
Application layer. The behavioral surface exposed by the system executing transactions: scheduling patterns, operational cadence, strategy composition, size distribution. Encryption has no effect here.
Consensus-Level MEV
In systems where a small, known, and trusted set of entities produces blocks, consensus-level MEV is a limited practical concern. In permissionless systems with open validator sets, the same assumption does not hold: a validator with economic incentives can reorder or insert transactions to extract value independently of any mempool-level protection.
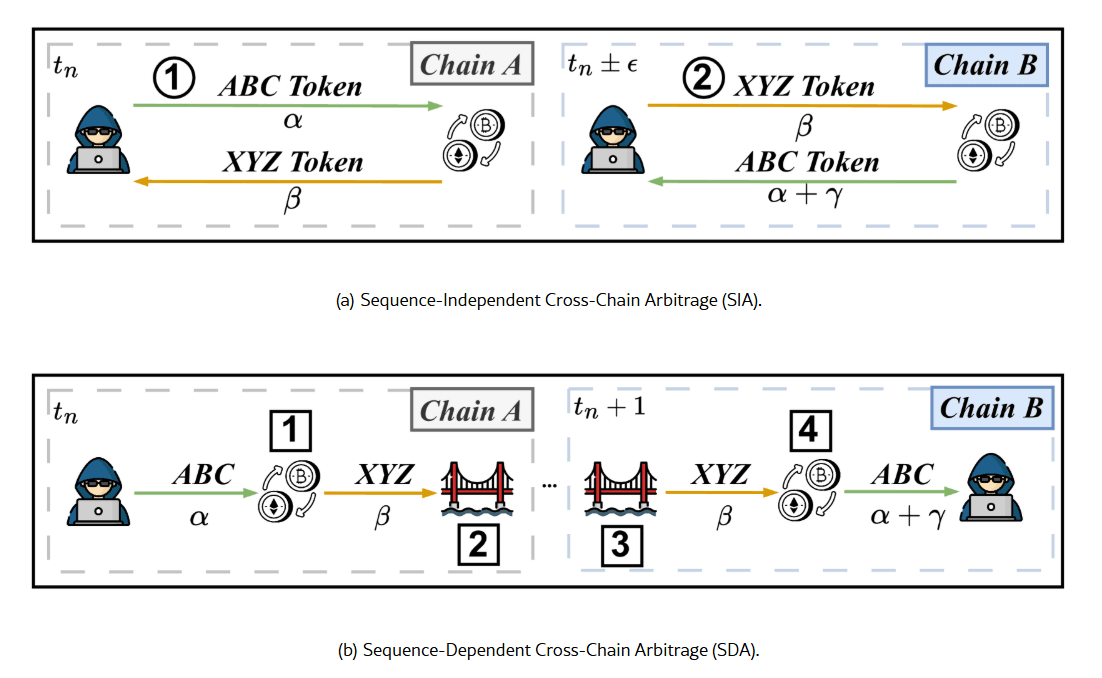
Reactive MEV
Reactive MEV requires reading the content of a pending transaction before it is executed. Front-running and sandwich attacks are the canonical forms: an attacker observes a target transaction in the mempool, infers its effect on price, and acts before or around it.
This is the problem encrypted mempools are designed to solve, and within its scope, the protection is structural.
Structural MEV
Structural MEV operates at the protocol layer and does not require reading transaction content. It exploits the mechanics of transaction ordering: how priority is assigned, how competing transactions are sequenced, and whether the protocol allows replacing a pending transaction before it is included.
An attacker operating in this space does not need to know what a target transaction does. Controlling relative position is sufficient to front-run or displace it. For example: an attacker who can place a transaction at the start of a block gains risk-free access to liquidation opportunities before any competitor can act.
The specific mechanics vary by protocol, but the common thread is that ordering rules, if they can be gamed, create extractable value independently of mempool encryption.
Anticipatory MEV: The Residual That Encryption Cannot Touch
Anticipatory MEV is the vector that survives encrypted mempools and protocol-level ordering fixes. It does not require transaction content visibility, only public information: on-chain history, observable cadence, inferrable strategy composition.
An attacker who can estimate the direction and timing of a future operation can take a position before execution and exit after the price impact, without ever reading a transaction.

The severity of exposure depends on how predictable the execution timing is and how reliably an attacker can estimate direction and size. Both variables are determined by the system's architecture and operational behavior, not by its mempool model.
Application-Level Mitigations
Mitigations for anticipatory MEV operate at the application layer. None eliminates the vector. Their collective effect is to increase the cost and uncertainty of pre-positioning until the expected payoff becomes statistically unprofitable.
Two categories of approach address different dimensions of the exposure.
Timing unpredictability. Reducing the precision with which an attacker can anticipate when execution occurs forces a longer holding period, increasing capital commitment and exposure to adverse price movement during the wait.
Size and impact distribution. Splitting operations across time and reducing the magnitude of any single event lowers the price impact available for extraction and makes individual operation sizes harder to estimate in advance.
The appropriate combination depends on the system's specific architecture.
Conclusion
Encrypted mempools close one attack surface, not the full stack. Structural MEV depends on protocol-level ordering rules. Anticipatory MEV depends on how much an attacker can infer from public data. Both survive mempool encryption and require independent evaluation.
The gap between what encryption protects and what operators assume it protects is where most unaddressed exposure lives. Closing it requires examining the full stack, and that work is necessarily protocol-specific.